It is the week everyone calls audit season, even though no season should feel this cold. A clinical lead exports screens into PDFs because someone heard the inspector prefers paper-shaped things. A QA manager rebuilds an approval trail from email because the electronic record points to a folder that moved. A GLP study director asks whether last quarter's hosting change means revalidation, and the only honest answer in the room is that nobody is sure until someone opens the binder.
That is not a failure of intent. Regulated labs are full of careful people. The friction shows up when documentation still behaves like a filing project while the work behaves like a live system. The gap between those two speeds is where nights get long.
We built Trust Vault on the Scispot platform to close that gap. Trust Vault is a structured compliance layer for teams who need to operate under continuous GLP, CAP, CLIA, and 21 CFR Part 11 expectations, with optional support when you want expert help executing IQ, OQ, and PQ alongside the product. The overview on scispot.com/trust-vault lists what ships today. This post is the longer story of why organized enough stops working the moment an inspector asks a precise question, and why we believe compliance belongs inside the same system where samples, studies, and signatures actually live.
The pressure regulators see even when they are not in the building
Clinical and GxP labs answer to a familiar set of forces: FDA inspections, CAP inspections, CLIA audits, sponsor audits, and the steady drumbeat of internal QA reviews. Each conversation has its own vocabulary, yet the underlying request repeats. Show how decisions were made. Show how data moved. Show who was allowed to touch it. Show how the system was qualified and how you know it still behaves.
When those questions arrive, the organization discovers whether its truth is retrievable or merely true in principle. A story everyone believes is not the same as a chain you can export on demand. That difference is expensive. It shows up as weekend reconstruction work, as tense conference rooms, and as risk that has nothing to do with science quality and everything to do with record design.
Sponsor audits add another layer. A pharma partner is not trying to be difficult. They are trying to sleep at night. They want to see segregation of duties, controlled documents, and traceability that does not depend on a single person's inbox. When your evidence is fragmented, you spend the audit proving you are organized instead of proving the science and the operations are sound.
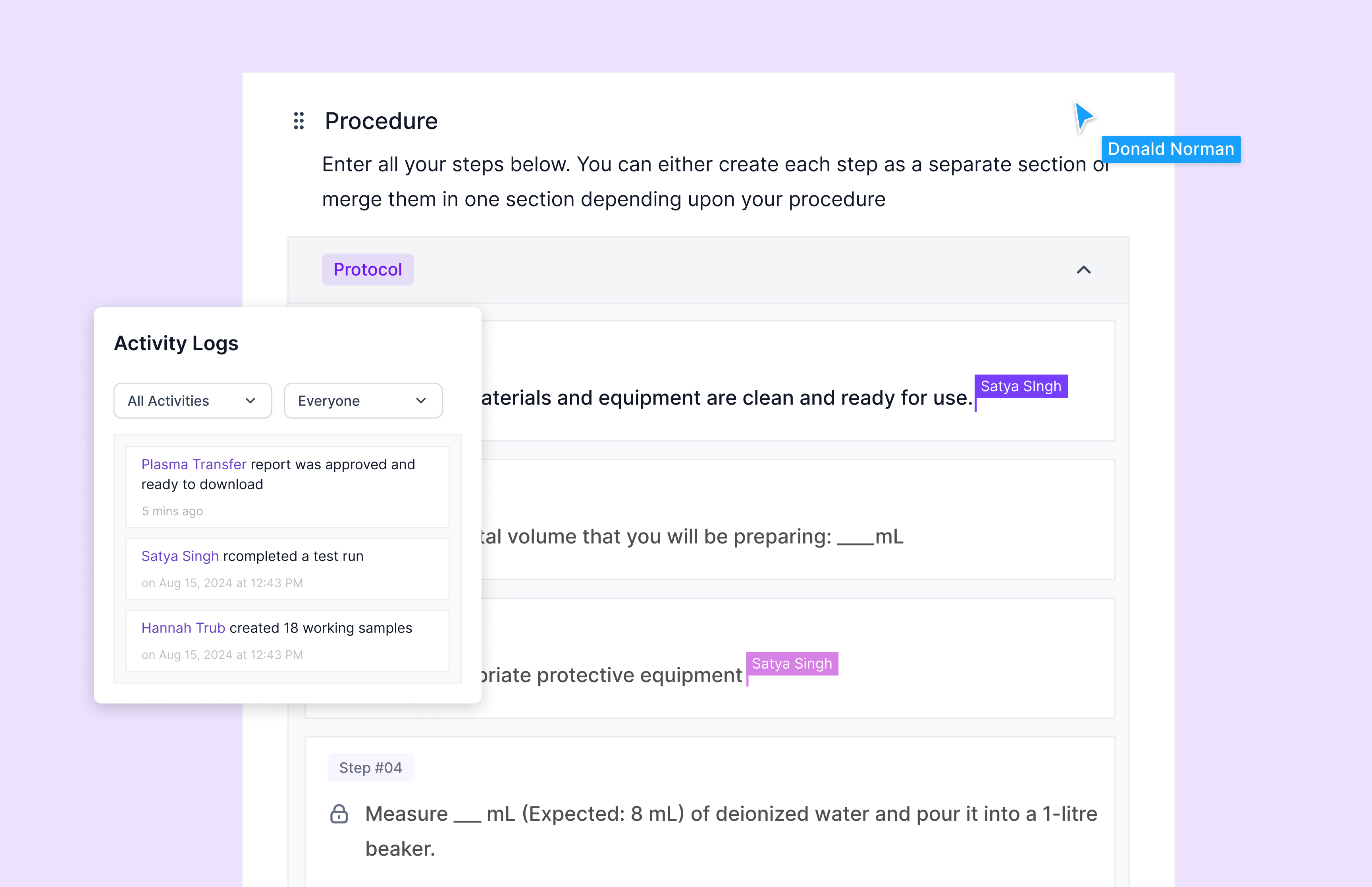
If you spend time inside Scispot asking for records, you already know what fast retrieval feels like when metadata, permissions, and history are first-class. Trust Vault extends that idea upstream into validation and inspection readiness: the point is not to make compliance theatrical. The point is to make it structured and continuous, so the next review does not become a bespoke archaeology project.
When documentation lives in folders and static files
Many teams still operate with good habits and brittle containers. PDFs in shared drives can be clear on day one and ambiguous on day six hundred. Spreadsheets are flexible until they become the unofficial database for equipment logs, training reminders, and calibration due dates. Version control for SOPs can live in file names until two teams publish two finals.
In that world, three failure modes appear again and again. Teams reconstruct audit trails manually because the system of record and the story of the record are not the same object. Teams rebuild IQ, OQ, and PQ summaries under pressure because the original execution was scattered across tickets, notebooks, and attachments. Teams revalidate without crisp triggers because change control is documented, but the link from change to qualification status is fuzzy.
It works until it does not. Then the cost is sudden. An inspector asks for a straight line from protocol to evidence. A sponsor asks how you proved performance under load. A CAP or CLIA review asks for QC traceability and maintenance history in a shape you can hand over without narration. If your answer requires three people and a map of where everything might be, you are paying a tax that never appears on a purchase order.
The cruel part is that many labs already did the hard work. They ran the tests. They approved the changes. They trained the staff. The missing ingredient is packaging: a coherent narrative that connects decisions to records without asking a human to become a search engine under deadline pressure.
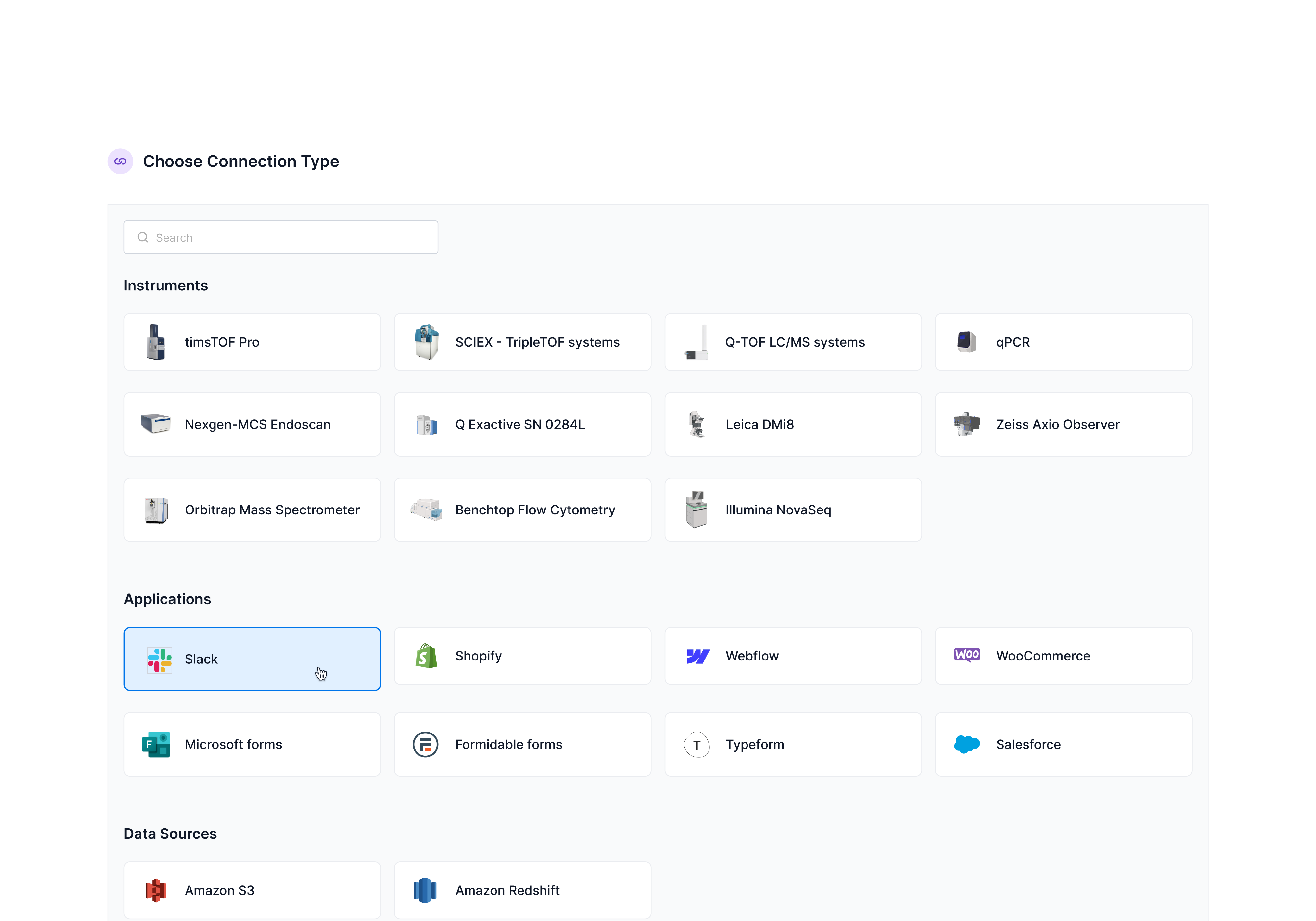
Why we anchored compliance inside Scispot
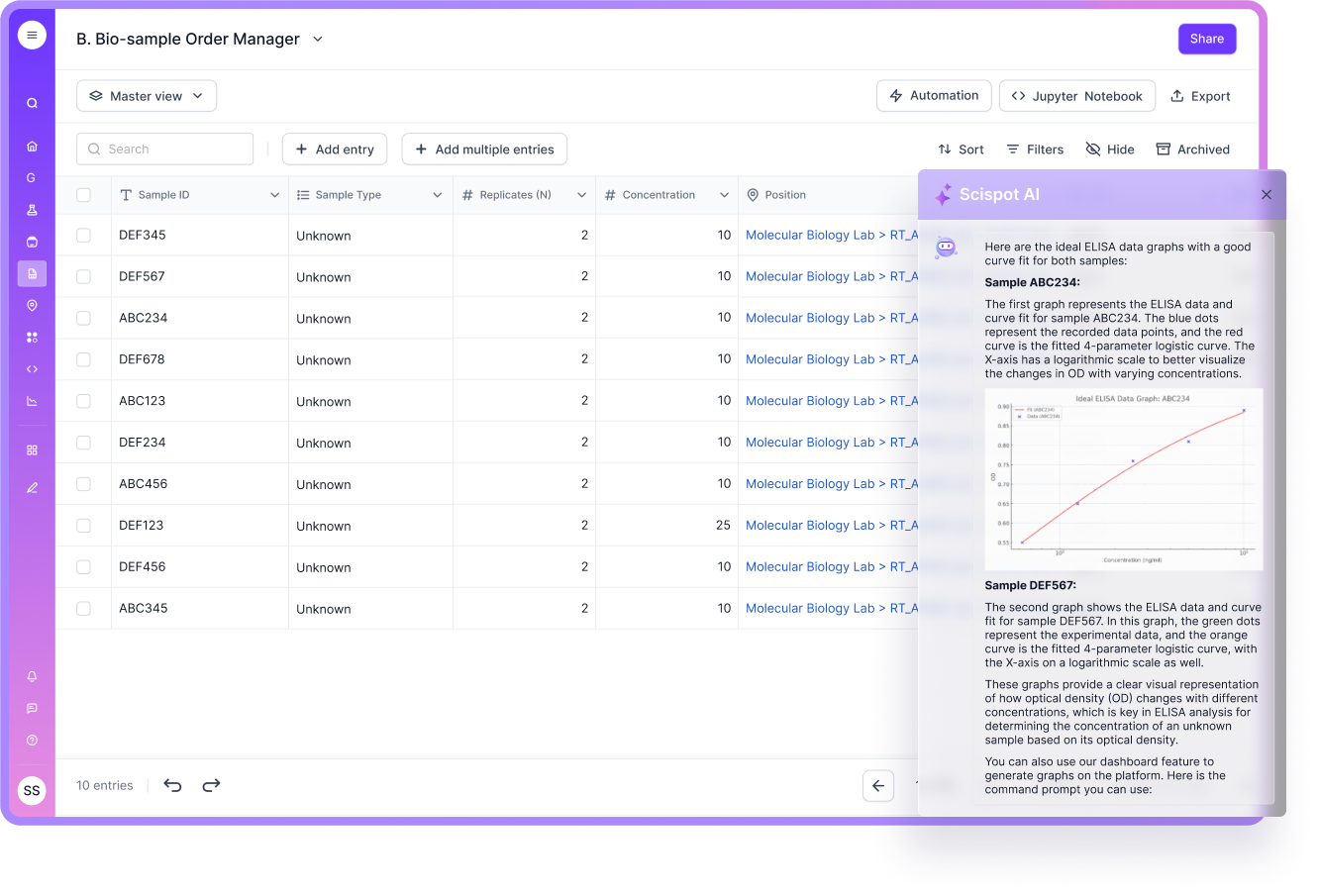
Scispot exists to unify lab data and workflows so high-throughput teams can run experiments, track samples, and collaborate without manual glue. The more faithfully the platform represents daily work, the more unreasonable it becomes to treat compliance as an outer wrapper that must be rebuilt whenever reality moves.
Trust Vault is our answer to that mismatch. Instead of treating validation and inspection readiness as a parallel paper universe, we structured it as a system you run alongside the same roles, objects, and audit semantics you already depend on for defensible operations. The goal is simple to say and hard to fake: when someone asks for proof, you retrieve it quickly because the proof was produced as part of the workflow, not assembled after the fact.
We heard the same pattern from quality leads and bench leads alike. Operators want software that matches how work happens. Quality wants software that makes defensibility ordinary instead of heroic. Trust Vault is where those two demands meet: structured artifacts and lifecycle thinking without asking scientists to become document clerks every quarter.
Structured IQ, OQ, and PQ you can run as a lifecycle
Installation, Operational, and Performance Qualification are not buzzwords. They are the language many regulated programs use to show a system was installed correctly, behaves as intended, and performs acceptably for real work. The pain is rarely the science. The pain is keeping the lifecycle coherent when protocols, evidence, and reports drift into different silos.
Trust Vault supports a documented workflow for IQ, OQ, and PQ so teams can generate the kinds of artifacts auditors expect: signed IQ protocols and reports, operational qualification traceability matrices, PQ performance summaries, and consolidated validation packages that tell one story instead of twelve partial stories. Your system should be deployed and documented in a way that holds when someone outside your team reads it cold.
That matters because qualification is not a ceremony you finish once. It is a baseline you defend over time. When the baseline is scattered, every change feels like a judgment call. When the baseline is structured, you can be deliberate about what a change triggers and what evidence you need next.
Think of it as reducing translation loss. Each time a protocol, a test result, and a signed report live in different places, you introduce seams. Seams are where questions multiply. Trust Vault is designed to keep the lifecycle threaded so the seams are intentional gates, not accidental gaps.
21 CFR Part 11 and data integrity controls
For teams subject to 21 CFR Part 11 expectations, the conversation is not abstract. It is about whether electronic records and signatures stand on the same ground as their paper ancestors, and whether you can reconstruct what happened without heroics. Trust Vault is designed to support validation of controls that auditors commonly probe: electronic signatures, role-based access control, audit trail reconstruction, backup and recovery documentation, and change control with deviation logs.
The practical goal is retrieval under stress. When an inspector asks for proof, you should not need a tour guide. You need a path. That path is easier when permissions, signatures, and history are native to the platform rather than copied into a narrative the week before a visit.
Data integrity language can sound abstract until you translate it into a Tuesday. It is the difference between knowing a result was changed and being able to show who changed it, when, and why. It is the difference between trusting a signature and being able to explain the controls around that signature. Trust Vault is meant to support those concrete demonstrations, not to replace your quality system.
CAP and CLIA inspection readiness
Clinical lab inspections have their own texture. Checklists are specific. Time is short. Questions route through QC, equipment, SOPs, and personnel segregation. Trust Vault is designed to support those workflows with structured evidence: patient sample traceability, QC documentation and audit trails, equipment maintenance and calibration logs, SOP version control with approvals, and role separation that maps to how real teams actually divide responsibility.
When CAP or CLIA reviewers request records, the win is measured in minutes, not morale. The organization should be able to produce structured evidence without rebuilding the lab's memory from scratch. That requires discipline, of course. It also requires software that does not fight you when discipline must become output.
In practice, inspection readiness often comes down to repeatability. Can you produce the same evidence next month the same way you produced it today? If the method depends on a senior tech's personal folder structure, you have hidden risk. If the method depends on objects, permissions, and logs inside the platform, you have something a new hire can learn and an auditor can follow.
Continuous compliance and re-qualification triggers
One of the quiet ways labs accumulate risk is guessing when revalidation is required. Major system upgrades, hosting or region changes, new GLP modules, and new protocol additions are all examples of moments that should produce a documented decision, not a hallway consensus. Trust Vault tracks lifecycle triggers so compliance stays ongoing instead of episodic.
Continuous compliance is not a slogan. It is an operational stance. It means your documentation can keep pace with change because change is captured where work happens. It means inspections become a test of your normal state rather than a performance of your best intentions.
It also means fewer surprises when the platform evolves. Teams adopt new modules when science demands it. Infrastructure changes when security demands it. Without a structured lifecycle, each event becomes a debate. With one, each event becomes a decision with an evidence plan.
Use Trust Vault on your own, or add expert validation support
Some teams want the system and the autonomy to execute qualification with their own quality org. Others want a partner who can help draft protocols, run tests, perform qualification under lab load, and consolidate GLP validation summaries. Trust Vault supports both postures. You can enable Trust Vault and run your program internally, or you can pair the product with Scispot validation expertise when bandwidth and timing matter.
Certification outcomes depend on your auditor and scope. Trust Vault does not replace professional judgment, quality culture, or the specifics of your regulated program. What it does is keep you organized and inspection-ready so your effort goes into substance, not scavenger hunts.
What to do next
If you are already on Scispot, start with the Trust Vault overview and map the modules you need first. If you are evaluating platforms, ask vendors the boring questions that predict audit week: where signatures live, how audit trails reconstruct, how qualification artifacts stay linked to releases, and how change control becomes evidence instead of folklore.
Bring your quality team into that conversation early. The best implementations align IT, operations, and QA on what must be provable, not just what must be usable. Trust Vault is built to reward that alignment because it treats compliance artifacts as part of the product surface, not an afterimage of it.
Compliance should feel less like a season you survive and more like a property of how you run the lab every day. That is the future Trust Vault is built for: structured, continuous, and fast to show when someone asks you to prove it.
Read the product details on scispot.com/trust-vault, explore the Scispot platform, and book a demo if you want a walkthrough with our team. For questions about rollout, validation scope, or account options, reach support@scispot.com.




.png)
.webp)
























.webp)
.webp)